7 High-Risk Events to Monitor Under GDPR: Lessons Learned from the ICO's BA Penalty Notice
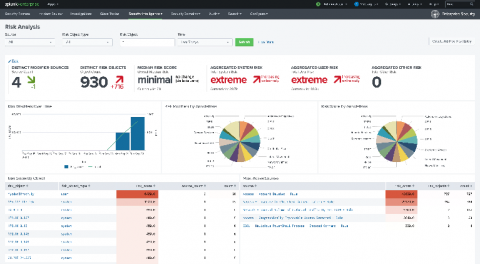
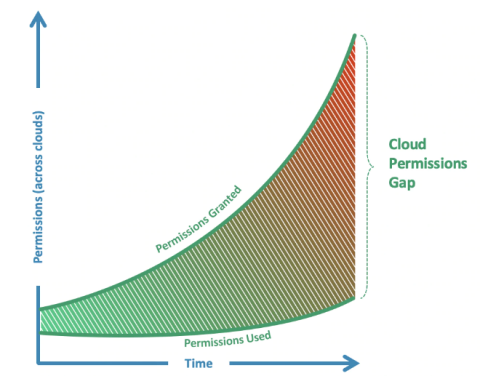
Hello Security Ninjas, Today's IT world is complex and can be challenging for security operations teams. Nowadays, more apps are being integrated and interconnected than ever before. Cloud services and SaaS solutions purchased all throughout the organization outside of the IT department add even more complexity. Communicating to application and service owners the kind of activities that need to be logged and sent to the SOC can be a daunting task.