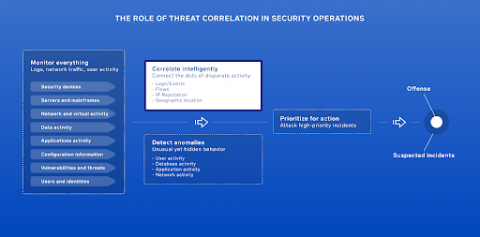
Sumo Logic advanced Cloud SIEM solution
In modern network security monitoring, it is not enough to just detect bad things happening. ROI of security operations is always under scrutiny. Security teams, when they exist, and their leadership (CISOs), continually struggle to get budget, at least until a public breach occurs.