Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Forescout
Rhysida Ransomware - Detecting a Significant Threat to Healthcare and Other Sectors
New TETRA:BURST Vulnerabilities Enable Attackers to Intercept and Inject Critical Radio Traffic - How to Mitigate Risk
You're Not Hallucinating: AI-Assisted Cyberattacks Are Coming to Healthcare, Too
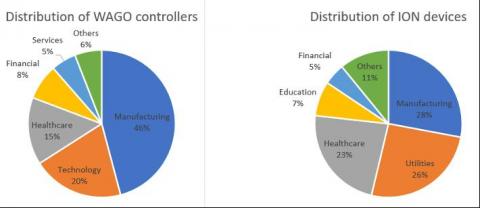
The 5 Riskiest Connected Devices in 2023: IT, IoT, OT, IoMT
Since 2020, Forescout Research – Vedere Labs has been tracking the riskiest devices on organizations’ networks. In 2020, we released the first Enterprise of Things Security Report, followed in 2022 with the Riskiest Connected Devices in Enterprise Networks report. Our reports are entirely based on data coming directly from connected devices.
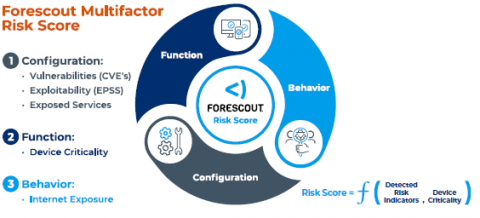
Go Beyond Device Visibility to Prioritize and Act on Cybersecurity Risk
When I joined Forescout as CEO six months ago, I was excited to partner with our strong employees, management team and board as we take the company through its next phase of growth. Today I’m pleased to announce enhancements to the Forescout® Platform that will help customers fully understand the risk posture of their attack surface and enable their security teams to focus on remediating the assets that pose the most risk.
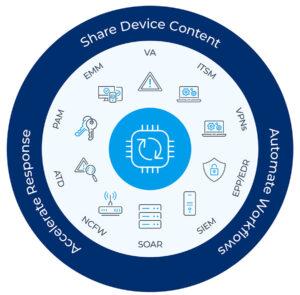
5 Steps to Combating Emerging Threats with Network Security
In today’s rapidly evolving threat landscape, cybercriminals have become more sophisticated than ever, making it crucial to stay abreast of the latest trends and tactics. The challenge is exacerbated by the expanding attack surface as more devices and device types connect to enterprise networks: IT, OT, IoT and IoMT devices, all with known vulnerabilities that can be exploited.
Lessons Learned from OT:ICEFALL - New Vulnerabilities and Insights on OT Security Design and Patching
In our final OT:ICEFALL report, Forescout Vedere Labs presents three new vulnerabilities and concludes the project after one year of research following the original disclosure. The OT:ICEFALL research, including 61 vulnerabilities affecting 13 vendors, has yielded three key insights into the current state of OT product security.
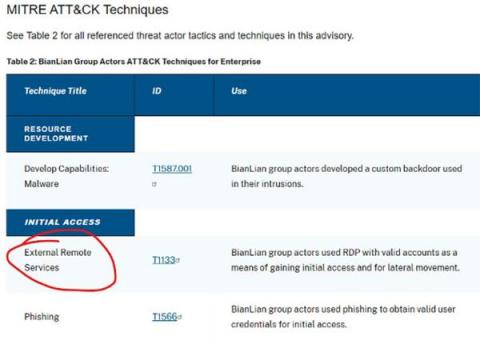
How Do You Know If You're Covered for TTPs in CISA Critical Advisories?
Depending on what the world’s threat actors are up to and whether their activity is detected, CISA may issue a cybersecurity advisory (CSA) every few days or have nothing for a month. It’s hard to predict, and you never know what’s coming your way. One thing is certain: If you managed cybersecurity for a critical infrastructure entity and this #StopRansomware: BianLian Ransomware Group CSA landed in your inbox, you would probably want to take swift action.
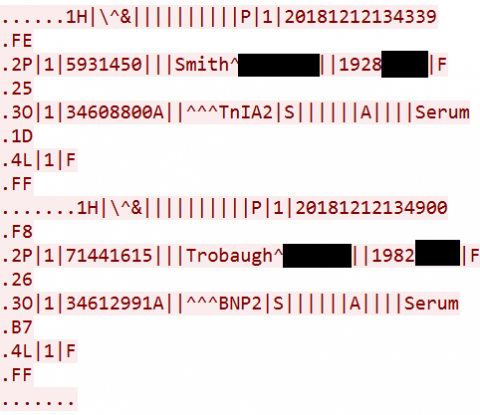
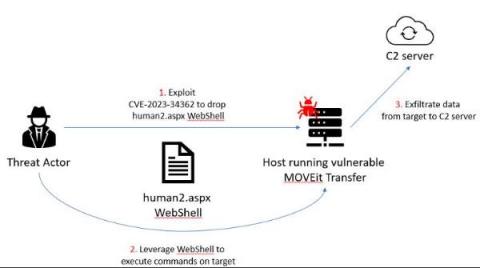
Mass Exploitation of MOVEit Transfer Critical Vulnerability - Recommended Mitigations and How Forescout Can Help
On May 31, Forescout Research – Vedere Labs uncovered a significant incident where threat actors exploited a critical zero-day vulnerability in the MOVEit Transfer software, which resulted in unauthorized access to and exfiltration of private data, as well as privilege escalation. MOVEit Transfer is a widely adopted managed file transfer (MFT) solution that enables organizations to securely exchange files with their business partners and customers.