Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Forescout
Cyber Skills Shortage? The Time for Security Automation Is Now
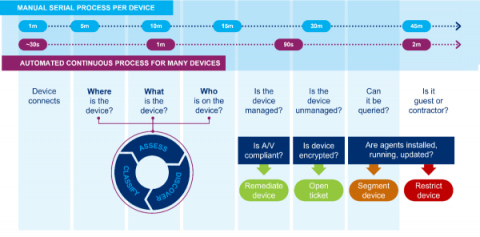
Many industries are affected by skills gaps, but according to Cybersecurity Ventures, the shortage within the IT/cybersecurity sector is nearly unmatched: Over an eight-year period, the number of unfilled cybersecurity jobs increased from one million positions in 2013 to 3.5 million in 2021.
Ransomware in Healthcare: The NHS Example and What the Future Holds
On August 4, 2022, Advanced – a major software provider for the UK’s National Health System (NHS) and other healthcare customers – suffered a ransomware attack from a group that is still unknown to the public. The attack disrupted NHS services including ambulance dispatch, appointment bookings, patient referrals and emergency prescriptions.
What to Do When Ransomware Meets the Internet of Medical Things
Vedere Labs recently developed a proof-of-concept (PoC) ransomware for IoT (R4IoT) using as an example attack scenario a hospital network containing IoT devices such as IP cameras, IT workstations and OT in the form of building automation controllers.
MAC Spoofing Detection with Forescout
Analysis of Clop's Attack on South Staffordshire Water - UK
On August 15, the Clop ransomware group announced on their leak website the breach of South Staffordshire Water, a privately owned UK water supply company. This attack is yet another example of ransomware gangs targeting critical infrastructure expecting to receive a big payout, which is reminiscent of hundreds of previous incidents, including the well-known Colonial Pipeline and JBS attacks.
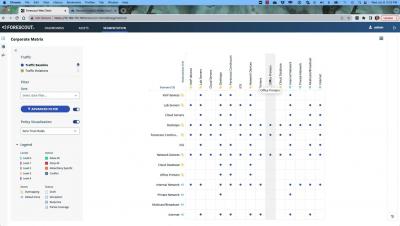
Automated Cybersecurity for Converged IT/OT/ICS Manufacturing Environments
For decades, IT and operational technology/industrial control systems (OT/ICS) were seen as separate entities within organizations. In keeping with practices first defined by the Purdue Enterprise Reference Architecture, the two systems were entirely air gapped to never impact one another. While this separation kept OT networks more protected, it is no longer practical.
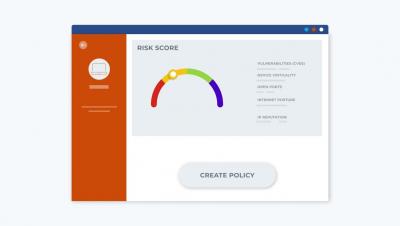
Forescout Multi-factor Risk Scoring
Accelerate the Journey to Zero Trust with Forescout and Arista
Improving Clinical Operations Efficiency through Network Analytics
In any organization and in largely any industry, most network analytics are driven by IT. Healthcare providers are no exception. The insights extracted via network analytics offer serious opportunities for operational improvements and added value across departments. There are also significant ancillary benefits from a more cyber-aware and “plugged in” organizational posture — including improved information sharing, collaboration, and security.