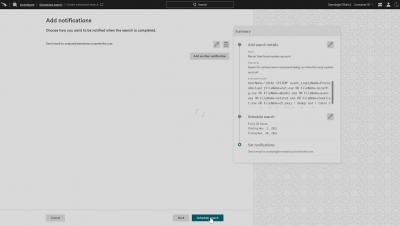
Accelerate Troubleshooting, Forensics and Response With Fast and Efficient Search
Whether you’re diagnosing a system outage, mitigating a malicious attack or trying to get to the bottom of an application-response-time issue, speed is critical. Pinpointing and resolving issues quickly and easily can mean the difference between success and crisis for any business, regardless of size or industry. Network and system administrators, security professionals and developers all depend on detailed log data to investigate issues, troubleshoot problems and optimize performance.