Multi-Cloud Security Best Practices Guide
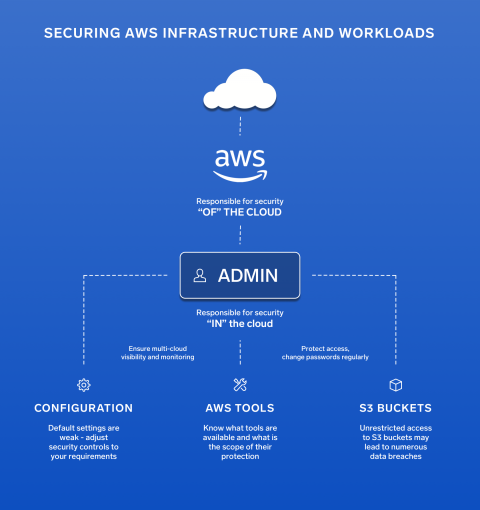
A multi-cloud network is a cloud network that consists of more than one cloud services provider. A straightforward type of multi-cloud network involves multiple infrastructure as a service (IaaS) vendors. For example, you could have some of your cloud network’s servers and physical network provided by Amazon Web Services (AWS), but you’ve integrated that with your servers and physical networking that’s provided by Microsoft Azure.