Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
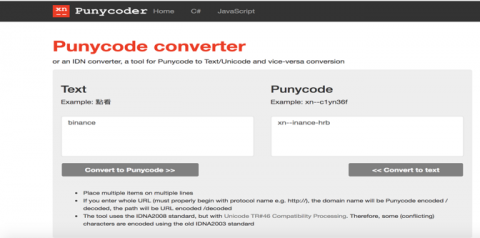
Domain Hijacking Impersonation Campaigns
Why is Cybersecurity Important?
Cybersecurity is important because cybersecurity risk is increasing. Driven by global connectivity and usage of cloud services, like Amazon Web Services, to store sensitive data and personal information. Widespread poor configuration of cloud services paired with increasingly sophisticated cyber criminals means the risk that your organization suffers from a successful cyber attack or data breach is on the rise.
Understanding the Purpose of Security Controls and the Need for Compliance
What are the brakes on a car designed to do? I have asked this question many times when speaking to customers or organizations who were dipping their toes into the audit space. Invariably, their answer was, “To stop the car.” At this point, I would then ask, “Then how do you get where you want to go?”
A Checklist for Preparing for Your Organization's Next PCI Audit
Organizations cannot afford to neglect their PCI compliance obligations. According to its website, PCI could punish offending organizations with a monetary penalty ranging in value from $5,000 to $100,000 per month. These fines could spell the end for a small business. Acknowledging those consequences, organizations need to make sure they’re PCI compliant. More than that, they must ensure they’re prepared for when auditors come knocking on their door.
Uncovering Bots in eCommerce Part 4: The Impact of Credential Stuffing
Credential stuffing is one of the most common forms of online crime, it is the act of testing stolen passwords and usernames against website login forms, to validate the credentials for malicious reuse. Once a match is found, the attacker can easily commit various types of fraud. When credentials are stolen through a database breach, malware, or other means, they are kept for use in future attacks against many different targets.
ISO 27001 Requirements Checklist: Steps and Tips for Implementation
ISO 27001 enables organizations of any size to manage the security of assets such as employee information, financial information, intellectual property, employee details, and third-party information. ISO 27001 is primarily known for providing requirements for an information security management system (ISMS) and is part of a much larger set of information security standards. An ISMS is a standards-based approach to managing sensitive information to make sure it stays secure.
DevSecOps for Kubernetes-based Applications
Ransomware observations
AT&T’s Digital Forensic Incident Response (DFIR) team has been observing cybercriminal organizations steadily increase their ransomware capabilities over the last few years. We have seen ransomware grow in sophistication and capability at a rapid pace. So rapidly in fact, that each investigation shows a new tactic or change in the binary program responsible for encrypting clients’ data.
Cybersecurity penetration testing explained
Cybersecurity penetration testing is a method of checking for security weaknesses in software and systems by simulating real-world cyber-attacks. Also known colloquially as 'pen tests,' penetration tests probe beyond the scope of automated vulnerability scans. Pen tests find gaps in protection that can arise when unique combinations of applications, systems, and security defenses work together in live environments.