Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
See Netskope Prove It
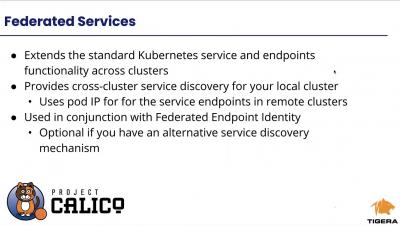
Multi-Cluster, Multi-Cloud and Hybrid Cloud Networking, Observability and Security Management
In the Financial Services Industry, 74% of Apps Have Security Flaws
Over the past year, the financial services industry has been challenged with pivoting its operations to a fully digital model, putting the security of its software center stage. Despite the unanticipated pivot, our recent State of Software Security v11 (SOSS) report found that the financial services industry has the smallest proportion of applications with security flaws compared to other sectors, along with the second-lowest prevalence of severe security flaws, and the best security flaw fix rate.
The Federal Office Has a New Look: Here's How to Keep it Secure
A Government Business Council report from September of this year found 63% of federal employees are fully remote, with many expecting to remain that way for at least the next six months. In this new reality, mobile devices have become a critical lifeline. But the mobile phones and tablets that keep us efficient and effective also open our organizations up to new risks against which existing security does not defend.
Attackers vs. Hackers - Two *Very* Different Animals
The cybersecurity industry is more well-informed than most, but even so, misconceptions arise and spread, helped along by the fact that the rise in cybersecurity incidents has led to substantial “pop culture” intrigue with all things cybersecurity. One of the more harmful of these misconceptions is the conflation of “hacker” and “attacker,” terms which are treated as interchangeable. They’re not.
Protecting PHI in Slack: Nightfall adds DLP (and value) to Perry Health
Pan Chaudhury created Perry Health in 2017 to streamline healthcare delivery. He and his co-founders envisioned a digital health tool to assist healthcare providers in managing chronic conditions like diabetes and hypertension by coordinating care and communication. Perry Health supports better healthcare outcomes by monitoring and engaging with patients when they’re not in the doctor’s office.
The roles and responsibilities that lead to better software security initiatives
If a project or initiative is going to be successful, it needs a plan spelling out what to do and how to do it. But that’s not enough. Somebody, or a group of somebodies, has to be in charge of getting it done. They have to own it. That’s the case with software security initiatives (SSIs), which are the focus of the Building Security In Maturity Model (BSIMM), the annual report by Synopsys.
Denmark's Largest Utility Company Accelerates Incident Response
As Denmark’s largest power, utility and telecommunications company servicing 1.5 million customers, Norlys understands the need for fast response to security alerts. When the company first started, the Norlys security team built their own log analytics and incident response capabilities from the ground up. This homegrown approach presented challenges, including manual workflows, too many repetitive tasks and difficult-to-maintain processes.