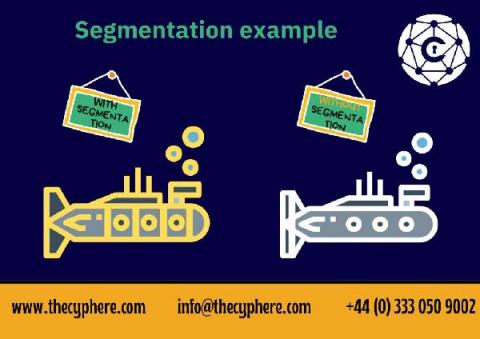
Network segmentation: Importance & Best Practices
Traditional and typical cyber security techniques usually fail to meet the security requirements of today’s corporate industries and businesses. As the digital world has revolutionized, so are cyber security threats and risks. It has become more difficult to rely on a single security solution or a single line of defence.