Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
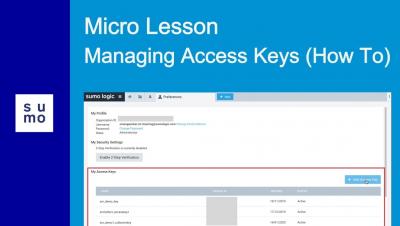
Micro Lesson: Managing Access Keys (how to)
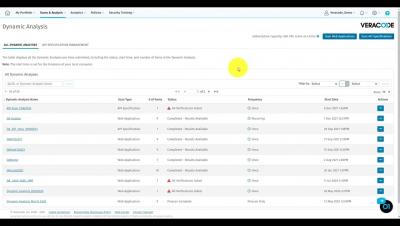
Review API Scanning Prescan Results
Safer Internet Day 2022: 4 tips to help support the youth in our lives
We all want a safer Internet, but we often put a lot of trust and hope in technology to deliver on that promise. The Internet is really made up of people, though. And people can make the biggest impact in creating a safer Internet. While everyone is impacted by Internet safety, children and youth are disproportionately at risk. The concept of a Safer Internet Day was born out of the desire to create a safer experience for young people.
Use Egnyte to Manage Partner Agreement Reviews and Approvals
Co-development agreements are an important part of the negotiation process between companies that partner to develop, sell, or commercialize products and services. In life sciences, these contracts often contain sensitive data, including pharma alliance collaborations for drug treatment innovations, or healthcare software integrations to enable digital health interoperability.
My 30 years of dodging repetitive work with automation tools
I blame my life-long work obsession with automation and avoiding repetitive drudgery on my first boss and mentor Danny in S3. He was horrified to see me doing the same thing over and over in a VAX code editor and introduced me to the magical world of macros. From that point onwards, I was a man on a mission to save us all as much time as possible in our working days.
Lessons from 2021: Damming the flood with micro-segmentation
We can’t always stop the bad guys from getting in, but we can stop them from wreaking havoc. Professor Avishai Wool, AlgoSec CTO, summarizes notable breaches from 2021 and explains the role of micro-segmentation.
GovCon Coffee Series: GovCon Cybersecurity With Eric Crusius | NeoSystems
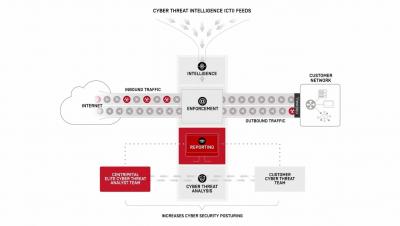
How Centripetal CleanINTERNET Works
Cyber Threat Analysis and Risk Assessment
Threat analysis and risk assessment (commonly referred to as TARA) are the key activities that should be carried out by all organisations whether they are enterprises or small scale companies. At present, there are many methodologies for how risk assessment and threat analysis can be performed.