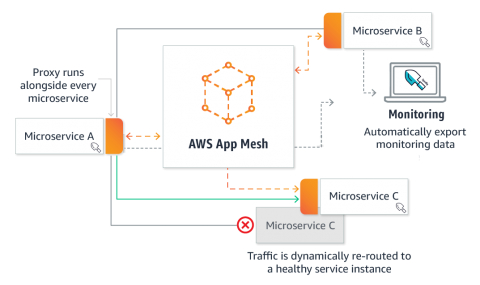
Providing Visibility and Security for AWS App Mesh
Microservice architectures running on containers have made applications easier to scale and faster to develop. As a result, enterprises are able to innovate faster and accelerate time-to-market for new features. To make management of microservices even more efficient and easier to run, service mesh solutions like Istio, Envoy, and Linkerd – and now AWS App Mesh – have become the next core building blocks of microservices infrastructure built on containers.