Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SecOps
What is a security operations center (SOC)? Explaining the SOC framework
If you’re responsible for stopping cyber threats within your organization, your job is more challenging than ever. The exposure to threats for any organization continues to escalate, and breaches are occurring every day. Consider: If your company doesn’t have a security operations center (SOC), it may be time to change that. In fact, a recent study indicates 86% of organizations rate the SOC as anywhere from important to essential to an organization's cybersecurity strategy.
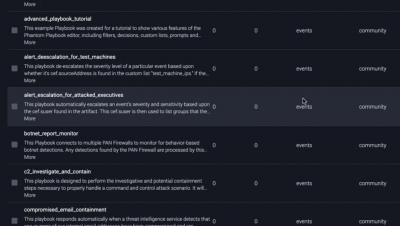
Splunk SOAR Feature Video: Playbooks
Orchestrate Framework Controls to Support Security Operations with Splunk SOAR
Every security team should utilize security frameworks in their strategy and tactics to help reduce risk from common cybersecurity threats. Security frameworks guide organizations on how they should develop, build, and maintain their IT security policies and procedures while sharing best practices for meeting compliance requirements. Healthcare operations in particular are often presented with increasing regulatory scrutiny and obligations that must be met in order to be competitive.
Stories from the SOC - DNS recon + exfiltration
Our Managed Threat Detection and Response team responded to an Alarm indicating that suspicious reconnaissance activity was occurring internally from one of our customer's scanners. This activity was shortly followed by escalating activity involving brute force activity, remote code execution attempts, and exfiltration channel probing attempts all exploiting vulnerable DNS services on the domain controllers.
Detection and Investigation Using Devo: HAFNIUM 0-day Exploits on Microsoft Exchange Service
On March 2, 2021, Microsoft announced it had detected the use of multiple 0-day exploits in limited and targeted attacks of on-premises versions of Microsoft Exchange Server. The Microsoft Threat Intelligence Center (MSTIC) attributes this campaign—with high confidence—to HAFNIUM, a group assessed to be state-sponsored and operating out of China, based on observed victimology, tactics and procedures.
Security operations center, Part 3: Finding your weakest link
Any organization with data assets is a possible target for an attacker. Hackers use various forms of advanced cyberattack techniques to obtain valuable company data; in fact, a study by the University of Maryland showed that a cyberattack takes place every 39 seconds, or 2,244 times a day on average. This number has increased exponentially since the COVID-19 pandemic forced most employees to work remotely, and drastically increased the attack surface of organizations around the world.
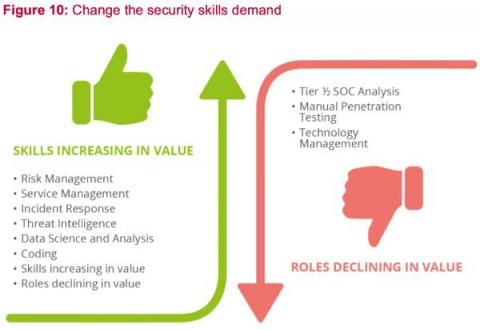
Building a Superstar SOC with Automation and Standardization
When you have a team of security analysts that have a wide range of expertise, knowledge, and experience, it is natural to see the difference in the quality of work performed. One of the biggest challenges that security operation managers face when auditing the work performed is that some team members may execute different steps at different levels of rigor when investigating and remediating threats.
Stories from the SOC - Beaconing Activity
Beaconing analysis is one of the most effective methods for threat hunting on your network. In the world of malware, beaconing is the act of sending regular communications from an infected host to an attacker-controlled host to communicate that the infected host malware is alive and ready for instructions. It is often one of the first indications of a botnet malware infection, so it’s important to spot the beaconing behavior before the infected host can expose data or launch an attack.
From the SecOps Kitchen: Why Operators of Essentials Services Need to Prepare Now
Hey there, The European Union Agency for Cybersecurity (ENISA) has recently published its NIS Investment report - a survey conducted on European organisations identified as Operator of Essentials Services (OES) and Digital Service Providers (DSP).