Vulnerabilities: The Gateway to Cloud Breaches
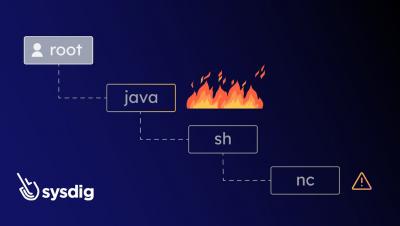
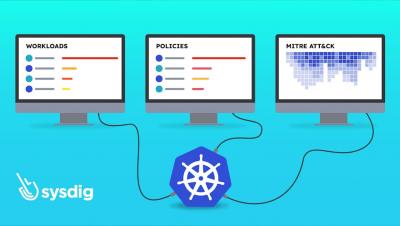
Things move fast in the cloud and cyber attackers are always on the lookout for vulnerabilities that they can exploit to gain access. In this short video, see the challenges faced by security teams in managing the ever growing list of vulnerabilities. Runtime insights provides the intelligence required to shift left - find and prevent vulnerabilities earlier, and shield right - protect what’s running in production.