Artificial Intelligence in Cybersecurity: Threat or Advantage?
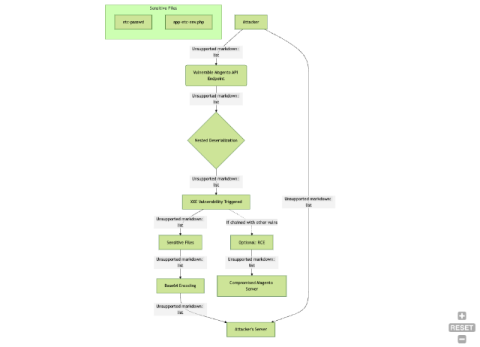
In today's hyperconnected world, cybersecurity stands as the first line of defense against the growing tide of cyber threats. With billions of devices connected globally, protecting sensitive information has never been more critical-or complex. Enter artificial intelligence (AI), a technological marvel capable of revolutionizing cybersecurity. But as with all powerful tools, AI is a double-edged sword. It holds incredible potential to bolster defenses yet can also amplify the capabilities of cybercriminals.