Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
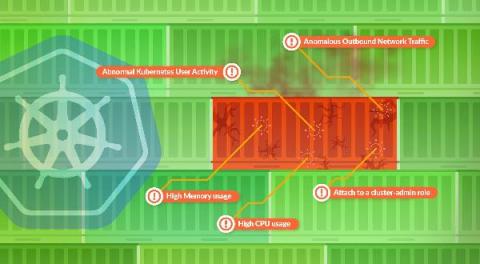
Top 10 Indicators of Compromise in Kubernetes
In this blog, you will learn how monitoring data from your Kubernetes environments can be used to detect indicators of a compromise in Kubernetes. Securing Kubernetes is challenging: Configuration flexibility, large clusters, ephemeral containers, and an ever-growing services ecosystem produce complex environments that open up your attack surface. Adversaries get an advantage because complexity is a natural enemy of security.
Hackers leverage RF to compromise smart TV remotes
This year’s RSA Conference was certainly a surprising one. There was an understandable focus, of course, on remote working security, alongside a relatively high number of presentations dealing with the issues of the moment – Kubernetes, the IoT, and the Biden administration’s plans for cybersecurity. In the midst of these headline presentations, it was easy to miss some of the less dramatic research, and even easier to miss its implications.
The state of SOAR: What to expect in 2021
Factors You Should Consider for an Optimal Hybrid Cloud Strategy
Cloud technology is a powerful tool with unmeasurable potential. Across the globe, companies are harnessing the cloud to propel their business solutions. However, there are always some companies that cannot entirely shift their solutions to the cloud. Thanks to the hybrid cloud model, companies house some of their solutions on their on-premises servers and store the rest of them in the cloud. Most companies have adopted the hybrid cloud model, as it suits both conventional and new-age operations.
CIS Control 2: Inventory and Control of Software Assets
Today, I will be going over CIS Control 2 from version 8 of the top 18 CIS Controls – Inventory and Control of Software Assets. Version 7 of CIS Controls had 10 requirements, but in version 8, it’s simplified down to seven safeguards. I will go over those safeguards and offer my thoughts on what I’ve found.
Leveraging Threat Intelligence and SIEM to See the Big Picture
Can you recall exactly how good or bad your vision was following your last eye exam? Most of us can’t. A casual poll around the office showed that many people focus only on whether our eye doctor says we need an updated prescription for glasses or contacts. Often, we walk away with a new script but without a clear understanding of our overall eye health, i.e., whether our eyesight got better or worse since the previous visit.
New banking paradigm requires better security paradigm
The digital shift is creating security challenges for the FSI. Learn how Synopsys tools and services can help get your security program back on track. Banking isn’t what it used to be—which means banking security can’t be what it used to be either. Keeping customers’ assets safe is no longer a matter of locking the massive door of a vault and keeping watch with some security cameras. The threats to security come from computer keystrokes, not masked men with guns.
5 Reasons we're seeing more ransomware attacks than ever before
Cybersecurity specialists have noticed several troubling trends over the past year, ransomware being one of the most concerning. While this is far from a new issue, it’s now more common than ever before. Every month in Q2 2021 set a new record for ransomware attempts, contributing to a 151% year-over-year increase compared to 2020. Cybercrime has risen in the past year, but ransomware attacks are outpacing other forms.
Learn Why Frost & Sullivan Names ThreatQuotient the XDR Competitive Strategy Leader
Extended Detection and Response (XDR) is the latest buzz word in the security industry and garnering significant attention. Industry analysts each have their own definition. Meanwhile, security vendors are quickly jumping on the bandwagon, recasting their products as XDR solutions. And it’s safe to assume many more will unveil XDR products in the months ahead.