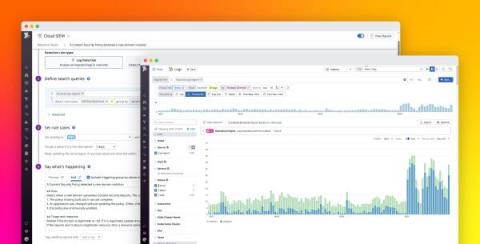
Monitor Content Security Policy violations with Datadog
Content Security Policy (CSP) is a W3C standard that helps defend web applications against cross-site scripting (XSS), clickjacking, and other code injection attacks. CSP is often deployed by using an HTTP header (or, less commonly, a element) to specify which types of resources are allowed to load on your site and where those resources can come from.