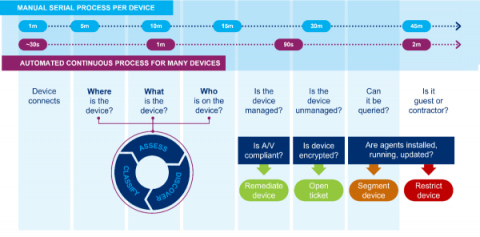
Cyber Skills Shortage? The Time for Security Automation Is Now
Many industries are affected by skills gaps, but according to Cybersecurity Ventures, the shortage within the IT/cybersecurity sector is nearly unmatched: Over an eight-year period, the number of unfilled cybersecurity jobs increased from one million positions in 2013 to 3.5 million in 2021.