Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
How to Prevent the Next Log4j Style Zero-Day Vulnerability
Software testing is notoriously hard. Search Google for CVEs caused by basic CRLF (newline character) issues and you’ll see thousands of entries. Humanity has been able to put a man on the moon, but it hasn’t yet found a proper way to handle line endings in text files. It’s those subtle corner cases that have a strong tendency of being overlooked by programmers.
PoC Exploit for Active Directory Certificate Services Vulnerability (CVE-2022-26923) Creates Path to Domain Admin
The importance of security automation
Security is a critical, if somewhat overwhelming, task for any organization. As products grow and teams expand, the challenge of maintaining a security posture at scale increases as well. This is where automation comes in. The ability to automate security tasks offers obvious benefits such as increased speed, while also driving deeper shifts in a company’s culture and processes.
Springing 4 Shells: The Tale of Two Spring CVEs
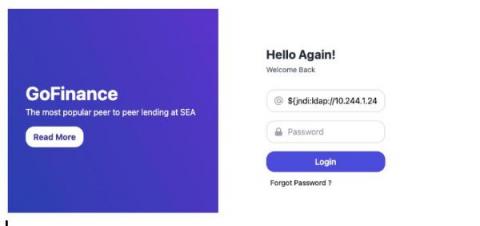
The Splunk Threat Research Team (STRT) has been heads-down attempting to understand, simulate, and detect the Spring4Shell attack vector. This post shares detection opportunities STRT found in different stages of successful Spring4Shell exploitation. At the time of writing, there are two publicly known CVEs: CVE-2022-22963, and CVE-2022-22965. The Splunk Security Content below is designed to cover exploitation attempts across both CVEs.
Impact Analysis: CVE-2022-29218, Allows Unauthorized Takeover of New Gem Versions via Cache Poisoning
It’s been a bad month for RubyGems vulnerabilities. Critical CVE-2022-29176 was issued May 8, 2022, and another critical CVE-2022-29218 was discovered less than a week later, on May 11. This new vulnerability would allow for a takeover of new versions of some platform-specific gems under certain circumstances.
Two-factor authentication misconfiguration bypass
Trustwave's Action Response: F5 BIG-IP Vulnerability (CVE-2022-1388)
Trustwave SpiderLabs is tracking a new critical-rated vulnerability (CVE-2022-1388) affecting F5 BIG-IP network devices. Threat actors are reported to be actively exploiting this vulnerability in the wild. F5 disclosed and issued a patch for CVE-2022-1388 on May 4. We are diligently watching over our clients for exposure and associated attacks and working closely with our clients to ensure that mitigations are in place.
Spotting Log4j traffic in Kubernetes environments
Editor’s note: This is the latest in a series of posts we have planned over the next several weeks where we explore topics such as network monitoring in Kubernetes, using sidecars to sniff and tunnel traffic, show a real-world example of detecting malicious traffic between containers, and more! Please subscribe to the blog, or come back for more each week.
FTSE 100 credential theft study 2022
Corporate credential theft is a targeted effort and makes FTSE 100 companies credentials particularly attractive to cybercriminals with accelerated digital transformation (BYOD and hybrid working). Once an attacker gets hold of stolen user credentials and passwords, they can sell the credentials in the cybercrime underground or use them to compromise an organization’s network, bypassing security measures and threaten the credibility and integrity of the institution.