Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
OT:ICEFALL Continues: Vedere Labs Discloses Three New Vulnerabilities Affecting OT Products - How to Mitigate
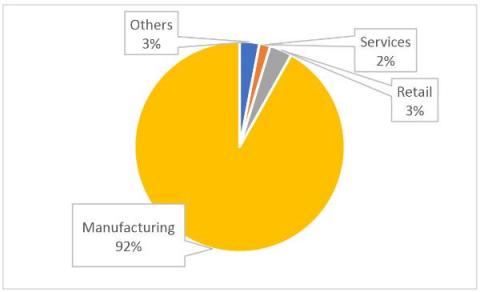
Continuing our OT:ICEFALL research, Vedere Labs has disclosed three new vulnerabilities affecting OT products from two German vendors: Festo automation controllers and the CODESYS runtime, which is used by hundreds of device manufacturers in different industrial sectors, including Festo.
10 AWS security considerations when migrating
Cloud data storage has many practical advantages over traditional data centers, but making a move also comes with many unique security considerations. When moving to AWS, begin how you wish to continue. Companies that transition to cloud data storage must update their approach to information security to protect their data. Setting up proper security practices during migration will help future teams securely and efficiently deliver applications and features.
Can gamification unite development and security?
Despite years of effort encouraging a DevSecOps approach, development and security teams tend to remain divided. For example, according to 2020 research, 65% of security professionals reported that their companies had successfully shifted security left. Good, right? But the same research also shows that almost a third of people believe the security team is primarily responsible for security — despite shifting left.
2022 Kubernetes Vulnerabilities - Main Takeaways
73 Percent Of Retail Applications Contain Security Flaws, But Only A Quarter Are Fixed
80% of SMBs Are Vulnerable - Here's How to Stay Safe
It would be nice to imagine that when cyber criminals look for their next target, they ignore the small- and medium-sized businesses (SMBs) that simply can’t afford an attack. Unfortunately, that’s not the case. In fact, 43% of cyber attacks are directed at SMBs. Today, a massive 80% of North American SMBs are at risk of a cyber attack.
How to use GitHub Actions environment variables
To improve the efficiency of releasing working code into a production environment, implementing a continuous integration and continuous delivery (CI/CD) pipeline is a great practice. These pipelines automate the process of checking that a code change is ready for release and provides tools to automate the release to a production environment. One popular way to do this is to use your existing version control system.
Top 10 Exploited Vulnerabilities in 2022
With each passing year, hacker attacks become more advanced and sophisticated, so keeping up with security vulnerabilities is now more crucial than ever. This article highlights some of the most dangerous vulnerabilities exploited by malicious actors in 2022.