EventSentry v4.0 - Introducing ADMonitor
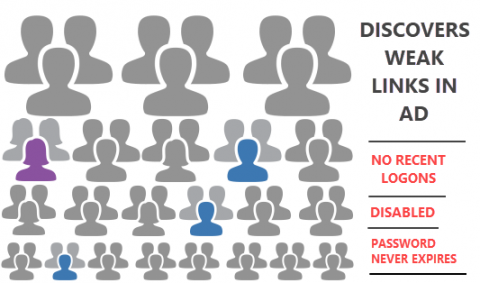
Since Active Directory is the foundation of all Windows networks, monitoring Active Directory needs to be part of any comprehensive security strategy. Up to version 3.5, EventSentry utilized Windows auditing and the security event log to provide reports on: User Account Changes, Group Changes and Computer Account Changes.