Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Posts
7 Challenges of Embedded Software Security Testing in 2023
We live in a world that depends on embedded software. It’s in the cars we drive, the elevators we take and the airplanes we travel in. As these systems become more and more complex, it becomes increasingly challenging to ensure that the interaction between embedded software and hardware remains functional and secure. Due to the nature of embedded systems and the devastating consequences of failures, many traditional testing methods fall short of providing adequate security for them.
An 8-Step Application Security Risk Assessment Checklist for 2023
As organizations are increasingly prioritizing application security continues to become a top priority for organizations, application security risk assessments is atop many bucket lists. Every application is unique and carries threats factors. It's critical to implement processes and tools to identify and remediate security issues before shipping.
3 Reasons Why You Should Fuzz Your Christmas Tree
A recent study shows that software attacks cause Millions of Christmas trees to go dark each year (Claus, 2021). Since many people believe that trees cannot be hacked, they tend to find themselves in a false sense of security that too often leaves them exposed. In this article, I want to show you why fuzzing is the right method to protect your Christmas tree against malicious software attacks while turning it into a video game console.
Top 10 Cybersecurity Conferences of 2023
2023 is coming in hot. If you don't want to miss out on this year's best events, you better start planning your conference schedule early. To help you out, I created an overview of my personal top 10 favorite cybersecurity events in 2023 about application security, cloud security, IoT, and all the other topics that currently occupy the cybersecurity world.
How to Fuzz Java with CI Fuzz CLI
All software has bugs, and some can be difficult to find or reproduce. However, not all approaches to bug-finding need to be difficult to use! Fuzzing is an undeniably effective approach to finding security issues and bugs in software projects, however, tools can be complex to set up and execute. CI Fuzz CLI (open-source), automates the parts that make fuzzing complex, giving its users the look and feel of a unit test.
Code Intelligence Unveils Simple Open-Source Tool to Automatically Test Java Applications for Unexpected Behaviors
Build Secure Java Applications with Fuzz Testing
Today, I want to show you a way how to increase the integrity and functionality of your Java applications, with fuzz testing. This awesome testing approach has done me great service for building more secure Java applications, and it's basically as simple as unit testing. In this article, I will share how you can apply fuzz testing to your own code. And the best part: all code examples and tools I will use are 100% open-source.
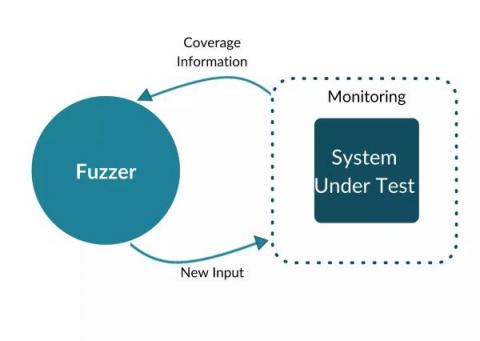
Mock Testing Embedded Systems With Fuzz Data
Mock testing, also called mocking, is an integral part of the embedded software development process as it allows you to test your code without relying on actual hardware. This can be extremely helpful when trying to debug your code or test new features. During fuzzing testing, applications are tested using unexpected or invalid inputs. Modern fuzzers generate these inputs based on feedback about the SUT’s interaction with previous test inputs.
The Benefits of Negative Testing in Software Testing
In software testing, negative testing refers to the practice of feeding a system with unexpected or invalid inputs. Given an input field that accepts numeric values from 0-100, positive tests would assess if the application does what it's supposed to do, given input values such as "1", "2" or "99".