Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Posts
Runtime Is The Way
Threat Detection on a Cloud-Native Attack Surface
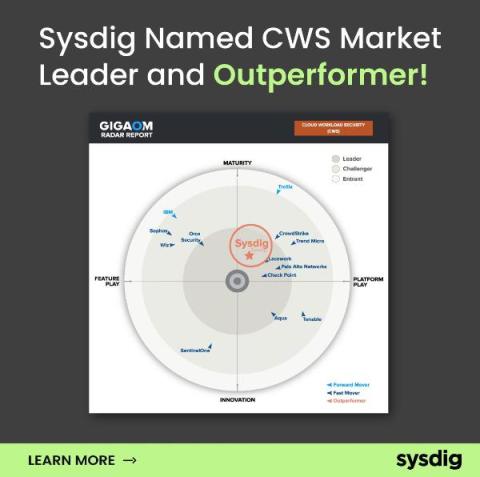
Sysdig Stands Alone: GigaOm Names Sysdig a Leader and Outperformer for Cloud Workload Security
How Financial Services Organizations Can Stay Compliant - Without Sacrificing Security
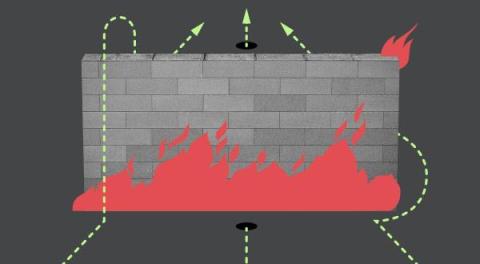
Fuzzing and Bypassing the AWS WAF
What's New - December 2023 Recap
Welcome to our December edition of the “What’s New in Sysdig” blog series. We decided to do a year in review for this monthly recap as we wanted to focus on a few key highlights the company went through the past 12 months. As we look at the past year, the landscape of cloud security has seen its challenges and evolution.
Honeypots with vcluster and Falco: Episode II
This is part two in our series on building honeypots with Falco, vcluster, and other assorted open source tools. For the previous installment, see Building honeypots with vcluster and Falco: Episode I.
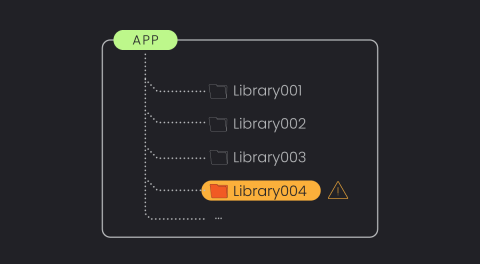
The Power of Library-Based Vulnerability Detection.
With an ever-growing number of vulnerabilities being discovered annually, vulnerability management tools are rapidly evolving to handle and prioritize these risks. However, it remains one of the most overwhelming and time-consuming areas in cybersecurity. There’s still significant room for enhancement, especially in reducing false alerts and prioritizing genuine threats.
Is Traditional EDR a Risk to Your Cloud Estate?
Organizations are transitioning into the cloud at warp speed, but cloud security tooling and training is lagging behind for the already stretched security teams. In an effort to bridge the gap from endpoint to cloud, teams are sometimes repurposing their traditional endpoint detection and response (EDR) and extended detection and response (“XDR) on their servers in a “good enough” approach.