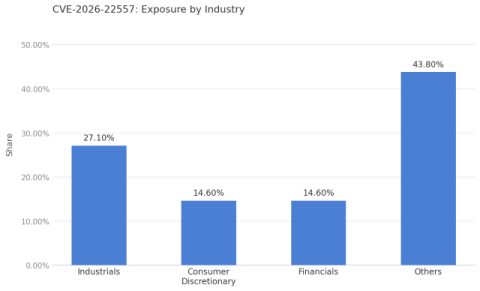
100,000+ New Vulnerabilities This Year and Most Will Be Zero-Days Exploited Faster
The number of publicly reported unique vulnerabilities has risen year after year. There was a brief decrease and stabilization in 2015 - 2016, but those are the only years in the over two decades (1999 - on) I have been following vulnerability metrics. Other than that, it has been up, up, up.