Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why Enterprises Need VAPT?
Splunk SOAR Playbooks: Conducting an Azure New User Census
In January and February of 2021, the threat actor called Hafnium used a number of post-exploitation tools after gaining access to Exchange servers through a zero-day exploit. One of their persistence methods was creating new user accounts in the domain, giving them the ability to log back into the network using normal authentication rather than use a web shell or continue to re-exploit the vulnerability (which has since been patched).
Defining Zero Trust Data Protection
The biggest fundamental shift in the era of digital transformation is that data is no longer on a CPU that the enterprise owns. Security teams focused on cloud must invest in the right technology to achieve more complete data protection, and we all need to ensure Zero Trust principles are applied everywhere data needs protection. At Netskope, we describe this as Zero Trust Data Protection. In its simplest form, Zero Trust means: Don’t trust the things you do not need to trust.
Sysdig Adds Unified Threat Detection Across Containers and Cloud to Combat Lateral Movement Attacks
Azure security 101: Security essentials, logs, authentication, and more
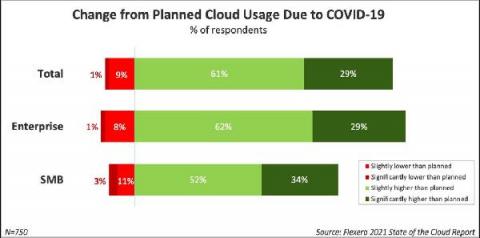
“Where necessity speaks, it demands”. This old saying seems particularly apt right now with the pandemic forcing organizations to completely change the way they think about their IT networks. That rapid shift to remote work has resulted in a massive demand for cloud-based services.
Survey: 99% of Security Pros Struggling to Secure Their IoT & IIoT Devices
Organizations are increasingly introducing new Internet of Things (IoT) devices into their environments. According to Statista, the aggregate number of IoT devices deployed by organizations globally increased from 7.74 billion in 2019 to around 8.74 billion a year later. The market and consumer data firm reported that the next few years will see growth in all types of IoT devices, including Industrial Internet of Things (IIoT) offerings like smart monitors.
Preventing Recent Microsoft Exchange Vulnerabilities and Similar Attacks Using Netskope Private Access
On March 2, Microsoft released patches to address four zero-day vulnerabilities in Microsoft Exchange Server software. Those vulnerabilities, known collectively as ProxyLogon, affect on-premises Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019. (Exchange Online, which is part of Microsoft 365, has not been affected.)
Getting started with cloud security
Unified threat detection for AWS cloud and containers
Implementing effective threat detection for AWS requires visibility into all of your cloud services and containers. An application is composed of a number of elements: hosts, virtual machines, containers, clusters, stored information, and input/output data streams. When you add configuration and user management to the mix, it’s clear that there is a lot to secure!