Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The growth of APIs attracts Cybercrime: How to prepare against cyber attacks
Application Programming Interfaces (APIs) have profoundly transformed the internet's fabric. In the pre-API era, digital interactions were limited by siloed systems functioning in isolation. APIs dismantled these barriers by introducing a universal language that diverse applications could comprehend. This linguistic bridge facilitated an unprecedented level of interconnectivity between software entities.
Accelerate Cloud Transformation with Netskope Borderless SD-WAN and AWS Cloud WAN
Navigating complex cloud networks with multiple clouds while ensuring secure and reliable access to workloads can be daunting. That’s why Netskope and AWS have teamed up to simplify this journey and make it a lot easier. Through the integration of Netskope Borderless SD-WAN with AWS Cloud WAN, teams can automate workload access from any remote site and user laptop, deliver a secure, reliable, flexible, and highly available middle-mile network service leveraging the AWS global network.
Build a 24/7 Security Operations Center (SOC) with Free and Open Source Technologies
Welcome to our comprehensive guide on building a 24/7 Security Operations Center (SOC) using free and open-source technologies. In the digital age, protecting your organization’s information assets has never been more important. Cyber threats are constantly evolving, and organizations of all sizes and industries are vulnerable to attacks.
Top Five Free and Open Source SIEM
In an age where cybersecurity is paramount, organizations must be vigilant in protecting their digital assets and sensitive information. Security Information and Event Management (SIEM) solutions are crucial in this endeavor, as they provide comprehensive visibility into an organization’s cybersecurity posture. While there are many commercial SIEM tools on the market, the pursuit of truly free and open-source SIEM solutions is gaining traction.
How to Choose Effective AI Tools for Cyber Security In 2023
If you are searching for ways to actualise benefits from cybersecurity AI tools or want to find out what AI tools will really make a difference in your SOC, you’re not alone. A World Economic Forum survey last year showed that almost half of all security leaders thought AI and machine learning would have the greatest influence on stopping cyber attacks and malware in the next two years. And that was before ChatGPT started an AI frenzy.
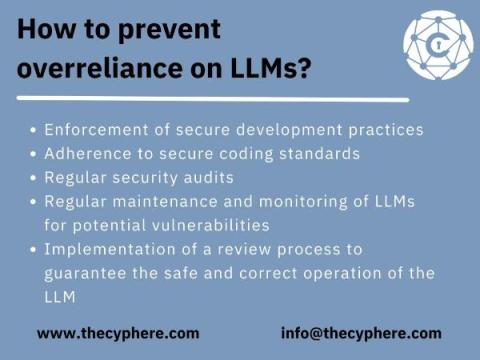
OWASP Top 10 for Large Language Models, examples and attack mitigation
As the world embraces the power of artificial intelligence, large language models (LLMs) have become a critical tool for businesses and individuals alike. However, with great power comes great responsibility – ensuring the security and integrity of these models is of utmost importance.
Bolster Amazon EKS security with Calico's image assurance capability
The integration of cloud-native technologies like Kubernetes with public cloud platforms like Amazon EKS has ushered in a new era of scalable and efficient application deployments. However, this combination brings forth unique security challenges, especially concerning container images. Enter Calico Cloud’s Image Assurance – a comprehensive tool designed to bolster the security of your containerized applications on Amazon EKS.
How Cloudflare mitigated yet another Okta compromise
On Wednesday, October 18, 2023, we discovered attacks on our system that we were able to trace back to Okta – threat actors were able to leverage an authentication token compromised at Okta to pivot into Cloudflare’s Okta instance. While this was a troubling security incident, our Security Incident Response Team’s (SIRT) real-time detection and prompt response enabled containment and minimized the impact to Cloudflare systems and data.
Small Screens, Big Risks: Falcon for Mobile Releases New Innovations to Accelerate Detection and Response for Mobile Threats
Mobile devices have become critical endpoints for accessing enterprise applications, systems and data. Adversaries know this all too well, as evidenced by the growing numbers of attacks that target mobile devices. Verizon’s 2022 Mobile Security Index found almost half (45%) of enterprises had recently suffered a mobile-related compromise involving devices in the last 12 months — almost double the amount compared to the year prior.