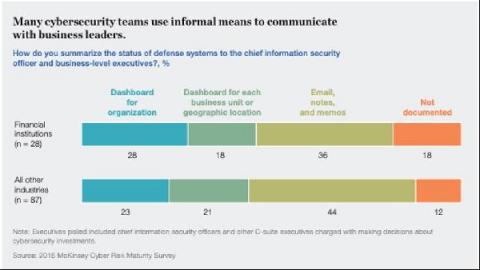
Where does cybersecurity fit in 2022 budget priorities?
As tech budgets start to return to a pre-pandemic state, it will be interesting to see where priorities have shifted to over the past year and a half – especially when it comes to cybersecurity. We’ve taken a look at a few major industry reports to give you an idea of shifting plans, and where cybersecurity sits as a priority in 2022 budgets.