Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
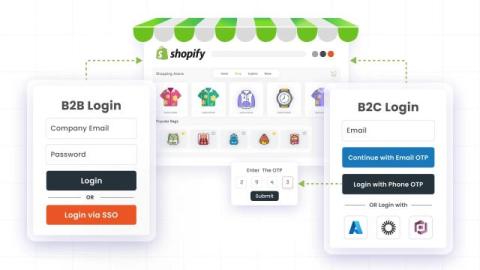
How to Implement Separate B2B and B2C Login & Onboarding in Shopify
Shopify stores are evolving beyond simple retail operations. What once was a primarily consumer-focused platform is now powering complex B2B experiences with tiered pricing, customer groups, and negotiated catalogs catering multiple B2B vendors and companies. However, as stores diversify their audiences, authentication becomes a critical pain point. A login flow designed for retail customers might be fast and convenient.
How miniOrange's GPT App Connects LLMs to Your WordPress Site
WordPress is entering a new phase in how websites are managed with the introduction of API Abilities and support for the Model Context Protocol (MCP). These updates allow WordPress core, plugins, and themes to clearly define the actions they support and how those actions should be executed. For the first time, WordPress can communicate its capabilities in a structured way that large language models can reliably understand.
What is Credential Stuffing? A Complete Prevention Guide for Enterprises
Credential stuffing attacks have become one of the most common, yet underestimated, cybersecurity threats facing businesses today. Even with strong firewalls and the latest endpoint protection, organizations still lose millions every year to stolen login credentials reused across accounts. What’s worse, these attacks often stay undetected until real damage occurs, which includes data breaches, customer account takeovers, and regulatory penalties.
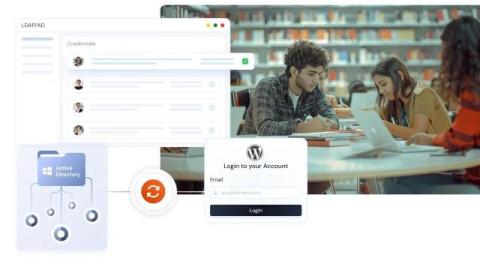
Making Student and Staff Logins Easy on WordPress with LDAP
Managing student and staff logins across different school systems can be messy and unmanageable, especially when every portal requires its own account and password. For WordPress-based education sites, it often means IT teams are stuck creating user accounts manually, resetting passwords, or dealing with duplicate profiles.
2FA For WordPress Membership: 2FA for Membership Sites
Imagine this: your WordPress membership site, thriving with exclusive content and a growing base of loyal members. But what if one breach could shatter trust, expose sensitive data, and compromise your revenue stream? That’s where WordPress Two-Factor Authentication (2FA) steps in as your ultimate defence. Let’s dive into how WordPress 2FA transforms your WordPress membership site into an impregnable fortress and why it’s a must-have for any modern membership platform.
User Provisioning and Data Synchronization - User Synchronization for WordPress
With the growth of any business or organization, the importance of data accuracy, consistency, and privacy is rising. Things that may seem like a minor data error or glitch can have a major negative impact on sales, decision-making, and customer retention.
Identity & Access Management (IAM) Metrics Every CISO Must Track in 2026
Consider a common scenario: Your organization has allocated millions toward firewalls, endpoint protection, and advanced threat detection systems. Your security operations team maintains continuous monitoring through sophisticated dashboards. Yet, despite these comprehensive defenses, an attacker can gain unauthorized access using nothing more than compromised credentials and a hijacked service account. This is where identity and access management metrics play a key role.
What to Look for in a PAM Solution: Essential Features and Requirements
Security breaches occur in 86% of cases because of unauthorized privileged credential access, while the PAM market reached $4 billion in 2025 because of rising identity-based threats which include ransomware and cloud sprawl. Organizations need to address their hybrid system problems and AI-based cyber threats during 2026 because their existing password storage systems fail to fulfill their requirements.
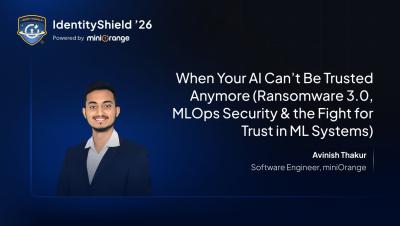
When Your AI Can't Be Trusted Anymore | IdentityShield '26
What if your ML system is running perfectly—but making the wrong decisions? This talk explores Ransomware 3.0, where attackers poison models and pipelines instead of locking systems, and shows how AI‑augmented attacks bypass traditional security and how to defend against silent ML compromise. Speaker: Avinish Thakur Software Engineer, miniOrange Pune, India.