Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
10 of the Most Significant Ransomware Attacks of All Time
For years, ransomware actors have developed new families and attack campaigns in increasing frequency and numbers. Such activity peaked in 2017 but then fell in tandem with cryptocurrency miners’ rise. This development was short-lived, however. Between Q4 2018 and Q1 2019, Malwarebytes observed a 195 percent increase in ransomware detections involving business targets. The rate was even greater compared to Q1 2018 at 500 percent.
Integrating Security to DevOps: Fundamental Principles Are Crucial!
Changing consumer demands posed a serious challenge to the IT industry; it pushed firms to brainstorm about quick product delivery. This demand eventually gave rise to the demand for collaboration between Development (Dev) and Operations (Ops) teams, welcoming the DevOps trend. As a result, everything started progressing well with increased development, enhanced collaboration, advanced testing, high productivity and minimized time to market.
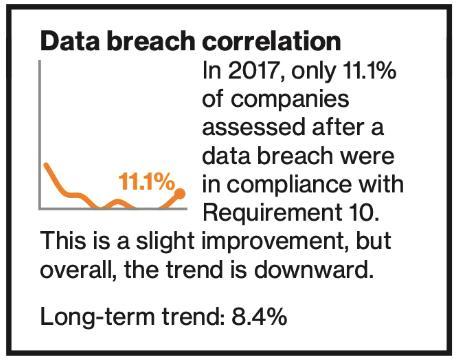
File Integrity Monitoring Best Practices
Nowadays, most of the IT systems use file-based architectures to store and process information. In addition, the critical applications such as operating systems, application binaries, configuration data of systems and applications, organization’s sensitive data, logs, and data which is pertinent to security events are stored in files. If any of these files is compromised, the financial and reputational damage occur to organizations.
Don't Trade Convenience for Security: Protect the Providence of your Work
I recently volunteered as an AV tech at a science communication conference in Portland, OR. There, I handled the computers of a large number of presenters, all scientists and communicators who were passionate about their topic and occasionally laissez-faire about their system security. As exacting as they were with the science, I found many didn’t actually see a point to the security policies their institutions had, or they had actively circumvented them. A short survey heard reasoning like.
Gamers risk getting played by hackers
If you’re in your mid-twenties or beyond, you will be familiar with people at family gatherings saying ‘remember when we didn’t have all these gadgets, and we used to actually talk to each other?’ The answer to this is ‘no’ – the level of conversation has remained largely unchanged, it’s just now we have gadgets and gizmos to occupy our attention during these moments of strained silence. I put it down to the Mandela effect.
Weekly Cyber Security News 06/09/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. A great example of (half) forgotten linked app this week via, quite unforgettably, from the Twitter CEO. I’m sure we all have linked services together as authentication of to bridge a data conduit just to do a trial or something and neglected to remove it afterwards. Well…. That lapse could come back to bite in the future.
Ransomware experiences and why IT security professionals have a lot on their minds
Every year we survey visitors to our booth at Black Hat about trending topics. This year, we asked about ransomware and the ever-increasing complexity of our cybersecurity environment. The results are very interesting - things may be getting much better, or we may all be collectively in denial. Let's break it down.
How we tracked down (what seemed like) a memory leak in one of our Go microservices
The backend developer team at Detectify has been working with Go for some years now, and it’s the language chosen by us to power our microservices. We think Go is a fantastic language and it has proven to perform very well for our operations. It comes with a great tool-set, such as the tool we’ll touch on later on called pprof. However, even though Go performs very well, we noticed one of our microservices had a behavior very similar to that of a memory leak.