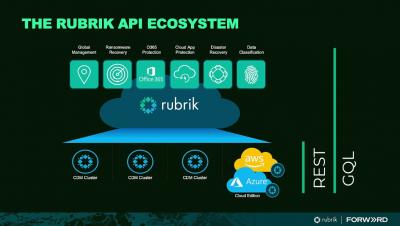
Cross Account Replication of AWS RDS with Rubrik Security Cloud
The Relational Database Service (RDS) service offered by AWS is one of the most popular databases today. A lot of critical, confidential data resides inside of RDS. Hence it becomes imperative to protect this data from various threats and ensure that the data is secure. Our approach to protecting the data inside RDS is based on two aspects: Rubrik already supports a modern approach to safeguarding RDS data from an operational perspective and also maintains a clean, secure copy in a different region.