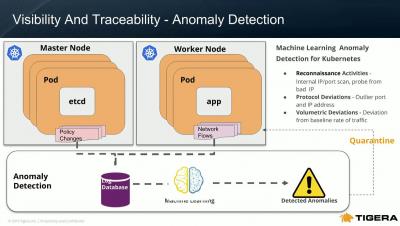
Complexity as the Enemy of Security
In an ideal scenario, security would be baked into the development process from the very beginning. Security teams would primarily exist to verify that best practices have been followed at every step in the process. In practice, security is an enormous challenge for most organizations. This challenge is compounded by the increasingly complex and fast-paced nature of modern service-oriented architectures, such as Kubernetes.