Quick FIX log management: How metadata simplifies financial protocol tracking (and how Corelight's platform can help)
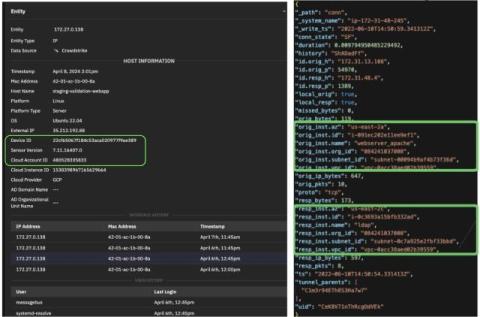
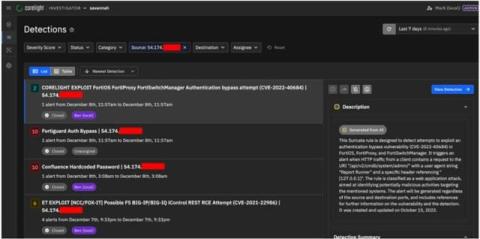
Financial institutions, such as banks and trading houses, have a strong interest in recording key transaction activity within their networks. In the face of daunting data storage requirements, many are finding that Corelight’s network metadata—notably metadata produced by Zeek—is the key to a simplified tracking and storage process. Many of our customers used to rely on packet capture (PCAP).