2022 Threat Roundup: The Emergence of Mixed IT/IoT Threats
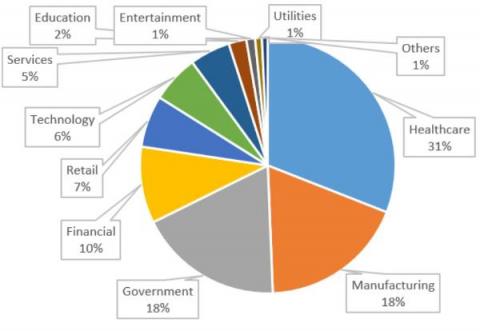
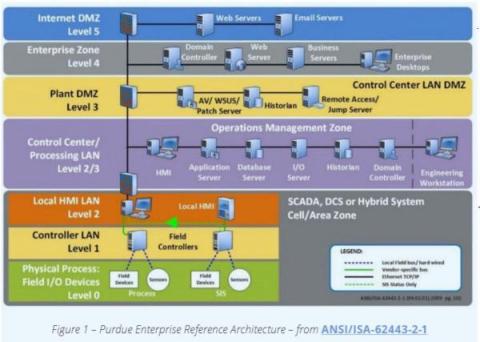
Rapid digitization means that organizations are now more connected than ever. Most organizations now host a combination of interconnected IT, OT, IoT and sometimes IoMT devices in their networks, which has increased their attack surface. Forescout’s data shows that around 24% of connected devices in every organization are no longer traditional IT.