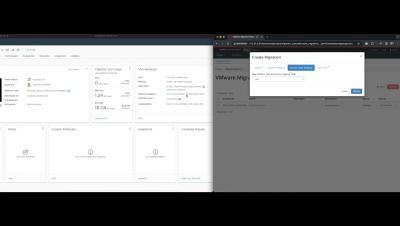
Full VM Recovery: Steps to restore your Virtual Machines completely
Full VM recovery can restore an entire virtual machine (VM) to its original state from a backup. It involves recovering all the VM’s components, including the operating system, applications, configurations, and data. With the Full VM Recovery option, you can restore the backup virtual machine/VM Template data to the same or different VMware host/server exactly in the same state as it was during the backup.