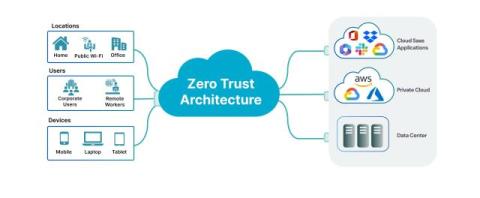
How to Protect Your IoT and OT Devices from Cyberthreats
The rise of the Internet of Things (IoT) and Operational Technology (OT) devices is reshaping industries, accelerating innovation and driving new efficiencies. However, as organizations increasingly depend on these devices, the security challenges associated with them are mounting. Traditional security measures often fall short in protecting these critical assets from cyberthreats, leaving organizations vulnerable to potentially severe disruptions.