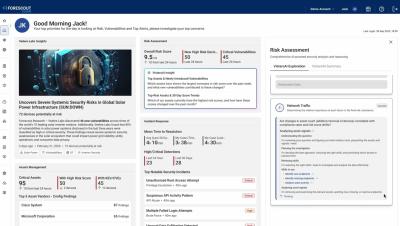
Forward Networks Expands Operations to Japan as Demand for Trusted Network Operations Accelerates
Forward Enterprise enables organizations to reduce risk, improve operational efficiency, and prepare their networks for trusted agentic AI and autonomous operations.