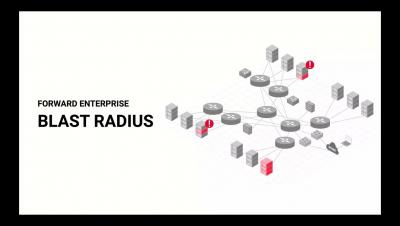
In High-profile OT Cyberattacks, the Culprit May Be the IT Network
Almost a year since the Colonial Pipeline ransomware attack on critical infrastructure occurred, the question still looms large: not whether such an incident could happen again, but when?