Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
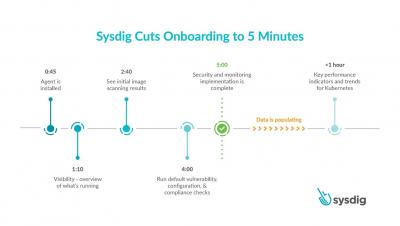
5 minutes to onboard secure DevOps
Egress access control for Kubernetes
12 Container image scanning best practices to adopt in production
Don’t miss out on these 12 image scanning best practices, whether you are starting to run containers and Kubernetes in production, or want to embed more security into your current DevOps workflow. One of the main challenges your teams face is how to manage security risk without slowing down application delivery. A way to address this early is by adopting a Secure DevOps workflow.
Detect CVE-2020-8557 using Falco
A new vulnerability, CVE-2020-8557, has been detected in kubelet. It can be exploited by writing into /etc/hosts to cause a denial of service. The source of the issue is that the /etc/hosts file mounted in a pod by kubelet is not included by the kubelet eviction manager, so it’s not taken into account when calculating ephemeral storage usage by a pod.
5 Risks You Need to Remember When Securing Your Containers
Containers are on the rise. As reported by GlobalNewswire, Allied Market Research estimated that the application market would grow from its 2016 value of $698 million to $8.20 by 2025. With a compound annual growth rate of 31.8% between 2018 and 2025, this increase would largely reflect both the surge in popularity in application container technology along with a growing number of organizations’ migration to the cloud.
Now GA: Data-in-Transit Encryption in Calico v3.15
We’re excited to announce that the latest release of Calico includes encryption for data-in-transit. Calico is the open source networking and network security solution for containers, virtual machines, and host-based workloads, offering connectivity and security for container workloads. One of Calico’s best-known security features is its implementation of Kubernetes Network Policy, providing a way to secure container workloads by restricting traffic to and from trusted sources.
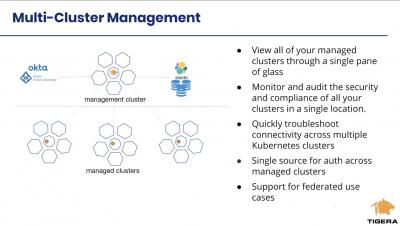
Introduction to multi cluster security using Calico Enterprise
Approaching Azure Kubernetes Security
The Splunk Security Research Team has been working on Kubernetes security analytic stories mainly focused on AWS and GCP cloud platforms. The turn has come now for some Azure Kubernetes security monitoring analytic stories. As outlined in my "Approaching Kubernetes Security — Detecting Kubernetes Scan with Splunk" blog post, when looking at Kubernetes security, there are certain items within a cluster that must be monitored.
File Integrity Monitoring: Detecting suspicious file activity inside a container
In this blog, we will explore suspicious file activity inside a container and see how to effectively implement a file integrity monitoring (FIM) workflow. We’ll also cover how Sysdig Secure can help you implement FIM for both containers and Linux hosts.