Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
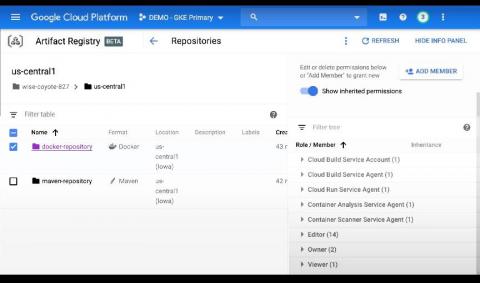
Sysdig extends image scanning to Google Cloud's Artifact Registry
In support of modern application development built on CI/CD, containers and open source, Google Cloud launched Artifact Registry (now generally available), a new artifact management solution. Sysdig helps DevOps teams using Artifact Registry confidently secure the build pipeline with comprehensive image scanning that identifies container vulnerabilities and misconfigurations to reduce risk.
Quick Intro: Sysdig Secure DevOps Platform
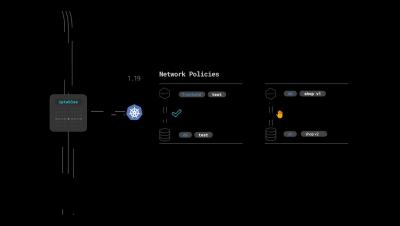
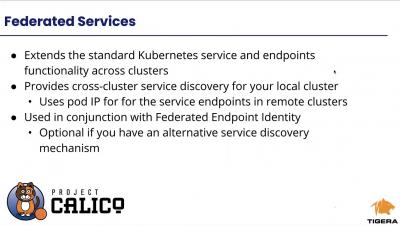
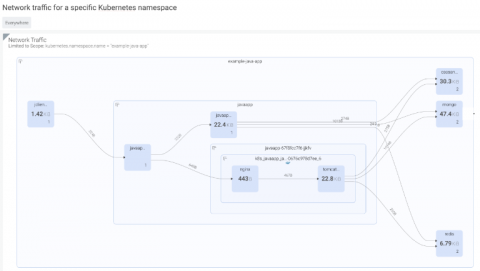
Multi-Cluster, Multi-Cloud and Hybrid Cloud Networking, Observability and Security Management
SOC 2 compliance for containers and Kubernetes security
This article contains useful tips to implement SOC 2 compliance for containers and Kubernetes. The Service Organization Controls (SOC) reports are the primary way that service organizations provide evidence of how effective their controls are for finance (SOC 1) or securing customer data (SOC 2, SOC 3). These reports are issued by the American Institute of Certified Public Accountants (AICPA).
How Containers Support the IT-OT Convergence
The worlds of information technology (IT) and operational technology (OT) are colliding. In July 2019, Automation.com cited a survey finding where 82% of respondents told Forrester and Nozomi Networks that their organizations were in the early stages of an IT-OT convergence. Some said their organizations were embracing this meeting more fully. This finding begs several questions. Why are IT and OT converging?
Understanding and mitigating CVE-2020-8566: Ceph cluster admin credentials leaks in kube-controller-manager log
While auditing the Kubernetes source code, I recently discovered an issue (CVE-2020-8566) in Kubernetes that may cause sensitive data leakage. You would be affected by CVE-2020-8566 if you created a Kubernetes cluster using ceph cluster as storage class, with logging level set to four or above in kube-controller-manager. In that case, your ceph user credentials will be leaked in the cloud-controller-manager‘s log.
Docker vs VMWare: How Do They Stack Up?
This is a clash of virtualization titans: one virtual machine, the other a containerization technology. In reality, both are complementary technologies—as hardware virtualization and containerization each have their distinct qualities and can be used in tandem for combinatorial benefits. Let’s take a look at each to find out how they stack up against each other, as well as how the two can be used in tandem for achieving maximum agility.
NIST 800-53 compliance for containers and Kubernetes
In this blog, we will cover the various requirements you need to meet to achieve NIST 800-53 compliance, as well as how Sysdig Secure can help you continuously validate NIST 800-53 requirements for containers and Kubernetes.
Session Control for SSH and Kubernetes in Teleport 4.4
Teleport 4.4 is here! The major innovation we’re introducing in this version is much improved control over interactive sessions for SSH and Kubernetes protocols. We’ll do a deeper dive into session control later, but for those who aren’t familiar with it, Teleport is an open source project. It provides access to SSH servers and Kubernetes clusters on any infrastructure, on any cloud, or any IoT device, anywhere, even behind NAT.