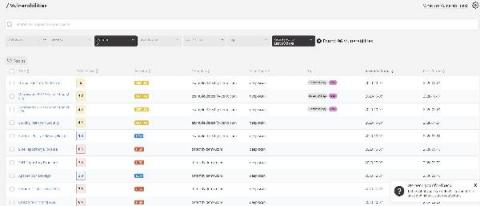
View and tag findings on the new vulnerabilities page to fix them faster
Triage is just as important to security teams as it is to hospital workers. Now, you can prioritize and remediate web application vulnerabilities even faster with tags and findings in one view for Detectify Deep Scan and Asset Monitoring. For the past couple of months, one of Detectify’s product teams has been working relentlessly on improving how customers consume security vulnerability findings.