GitGuardian Secrets Detectors Q1 2023 Wrap-Up
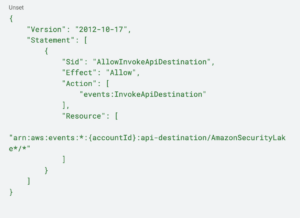
GitGuardian's Q1 wrap-up highlights our progress in detecting secrets, introducing new secret detectors, and committing to code security. With six new detectors released in Q1, GitGuardian remains the go-to solution for developers looking to write more secure code.