Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Difference Between Authentication and Authorization
Authentication and authorization are two complementary and critical parts of securing cloud-native applications and infrastructure. Yet, there can be some confusion between these terms. The importance of cybersecurity approaches, such as Zero Trust and the principle of least privilege, make it critical to understand and implement appropriate authorization and authentication processes across cloud-native development.
CrowdStrike Achieves Red Hat OpenShift Certification: Streamlining Visibility and Automating Protection for OpenShift
As organizations expand their cloud-native initiatives and increase their use of containers and Kubernetes in production, they face challenges regarding container security, monitoring, data management and networking. To meet this growing need, we’re pleased to announce our certification of Red Hat OpenShift through the CrowdStrike Falcon® platform — giving joint customers comprehensive breach protection for OpenShift nodes, workloads and containers.
Cyber Risk Intelligence: County Government Cyber Incident May Have Involved Social Engineering and Targeting of Vulnerable SSH Services
The government of a U.S. county announced on September 11 that a recent cyber incident had disrupted its online services. Subsequent coverage of the event has noted that it strongly resembles a ransomware attack. The disruption comes against a backdrop of frequent ransomware activity targeting state and local governments and the education sector.
Five Password Management Best Practices to Keep You Safe
Love them or hate them, passwords are often the only thing standing between attackers and your sensitive personal and financial information. Despite their importance, less than 50% of people feel very confident that their passwords are secure from compromise, according to a 2021 Security.org survey of password habits. There’s probably a good reason many are worried about their passwords.
Nightfall launches the first and only DLP solution for Asana
Today, we are delighted to announce that Nightfall has launched the first and only DLP solution for Asana. As part of this launch, Nightfall has joined the Asana Partner program as an official Technology Partner. Nightfall’s solution for Asana builds comprehensive data protection into the Asana app.
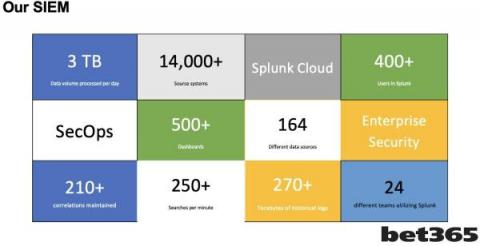
Inside the SecOps Team at bet365: Moving your SIEM to the Cloud
Hello, I love to look behind the scenes of SecOps teams to learn how they operate. Recently I had the pleasure to work with John Eccleshare, Head of Compliance and Information Security, at bet365 as John took the stage at Gartner Security and Risk Summit in London.
Federated Search for Security
Splunk introduced Federated Search in July 2021 to much fanfare. We won’t go into too much detail about how it works because there is already a great writeup in a previous blog along with Splunk Federated Search documentation.
Datadog alternatives for cloud security and application monitoring
Monitor your firewalls on the go with Firewall Analyzer's mobile app
The number of cybersecurity events faced by companies and businesses across the globe has grown exponentially since the pandemic began. Without adequate network security monitoring practices and around-the-clock monitoring in place, the chances of a cyber incident happening are highly likely. However, not all companies can afford to have a team of highly trained network admins watching over their network 24×7.