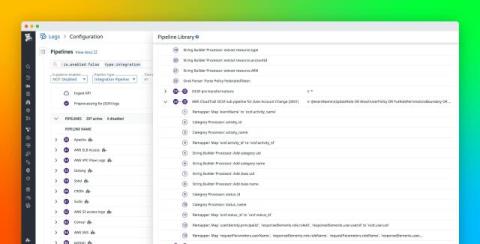
5 Ways CISOs Can Boost Operational Clarity
“CISOs and SOC analysts are fighting the same war, but too often, one’s answering to the board while the other’s drowning in alerts.” Security teams rarely fail because of a lack of skill or commitment. They fail when the coordination layer between the boardroom and the SOC starts to unravel.