Ransomware Attacks and Remediation Strategies for Financial Institutions
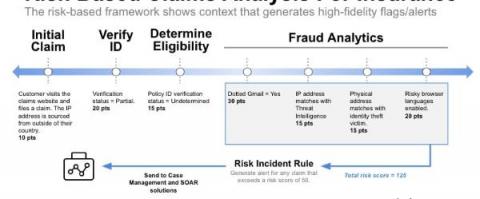
Believe it or not, the Financial Services industry has one of the slowest vulnerability remediation rates, with a median of 426 days. “Financial regulators can no longer rely on static, point-in-time assessments to understand the cybersecurity risks posed to the financial system,” said Sachin Bansal, SecurityScorecard’s Chief Business and Legal Officer, in a recent BusinessWire article. “Continuous monitoring tools must be a part of every regulator's toolbox.”