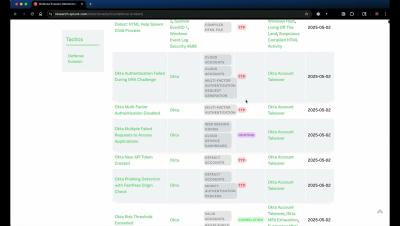
Understanding the MITRE ATT&CK Framework: A Modern Lens on Adversary Behavior
The MITRE ATT&CK framework is one of the most widely adopted and respected resources in the field of cyber threat intelligence. Serving as a common language for security professionals across industries and departments, it provides a consistent and structured way to describe adversary behavior.