Why Legacy DLP Fails and What Cyberhaven Does Differently - Full Video
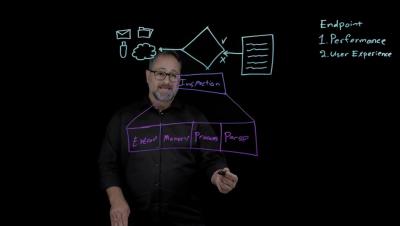
In this lightboard session, we break down how organizations classify and protect sensitive data—and why traditional methods fall short. You’ll see how Cyberhaven reimagines data security with lineage-based protection that works across files, systems, and formats. Watch to learn: The difference between data maps, tags, and labels The limitations of legacy classification (persistence & breadth)