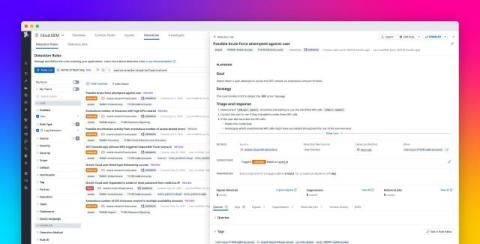
Monitor OCI Audit Logs with Datadog Cloud SIEM
Oracle Cloud Infrastructure (OCI) provides compute, storage, networking, and database services for running enterprise applications and workloads in Oracle. OCI supports both traditional and cloud-native applications, offering scalable, secure, and high-performance infrastructure for hybrid and multi-cloud environments. Securing workloads in OCI can be complex for organizations managing a mix of on-prem, hybrid, and cloud environments.