Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
A Complete Guide to Cybersecurity Compliance
Cybersecurity has become a top priority for organizations across all industries and sizes. To safeguard their sensitive data and assets from the ever-evolving threats of cyberattacks and data breaches, businesses must take a proactive approach. Adherence to industry-specific cybersecurity regulations and frameworks is a critical component in building a robust and comprehensive cybersecurity program.
Trustwave Action Response: Supply Chain Attack Using 3CX PABX Software
On March 29, a massive supply chain compromise in 3CX software resulted in malware being installed globally across multiple industries. It is similar to the other high-profile supply chain attacks (like SolarWinds and Kaseya) in that rather than targeting a single organization, the criminals target a popular service or software provided to many large organizations. With one single compromise of the supplier, dozens and potentially hundreds of organizations may fall in turn.
The Power of Continuous Penetration Testing
As organisations continue to become more reliant on technology, cyber security threats become more frequent and sophisticated. With more and more data being stored online, it’s crucial that organisations protect their systems and data from cyber attacks. Penetration testing is an effective way to identify vulnerabilities and weaknesses in an organisation’s cyber security defences, but traditional penetration testing has limitations.
Ultimate Security Checklist to Launch a Mobile App in Mexico - iOS & Android
Mexico is a budding market for mobile apps. The total revenue generated by mobile apps is expected to surpass $2100 million by 2027 from just $1500 million in 2022. So, if you're an app developer and thinking of launching a secure mobile app in Mexico, you're making the right decision. However, it's not as easy as you may think. Navigating Mexican data privacy regulations can be challenging, but it's critical to ensure that personal information stays secure and is not misused.
What Is the Dark Web and Is It Dangerous?
How To Prevent Overprivileged Data Access From Harming Your Business
Privileged access management was designed to prevent human errors and reinforce security in general. However, even though this approach has been used for decades, studies still show that human error contributes to 95% of cyber attacks. So what are organizations doing wrong? Are they using privileged data access in the best way possible? Sadly, many companies don’t put much thought into using their security systems correctly, but there is an easy way to fix this.
How Falcon OverWatch Investigates Malicious Self-Extracting Archives, Decoy Files and Their Hidden Payloads
Self-extracting (SFX) archive files have long served the legitimate purpose of easily sharing compressed files with someone who lacks the software to decompress and view the contents of a regular archive file. However, SFX archive files can also contain hidden malicious functionality that may not be immediately visible to the file’s recipient, and could be missed by technology-based detections alone.
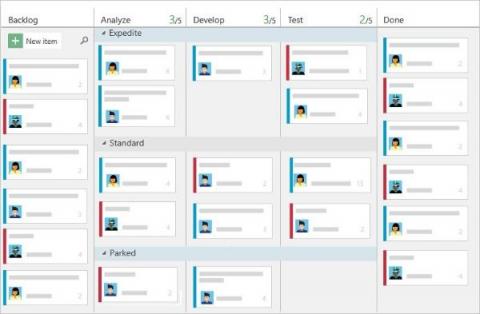
Working with Bytesafe Issues and Azure Boards
The need for secure coding practices has never been greater. Vulnerabilities can be introduced at any stage of the software development life cycle and can result in significant data breaches and other security incidents. Therefore, it’s essential to have a robust security process in place to catch these vulnerabilities early on. Bytesafe is a security-focused tool designed to help developers and organizations secure their software development process.
Ferrari Gets Hit by a Cyber Attack, Exposing Customers
Ferrari is a well-known luxury car manufacturer based out of Italy. The company creates some of the most beloved sports cars and is known for producing vehicles that stand out for their beauty and performance. The company began in 1947 and had been producing head-turning vehicles ever since. Ferrari is well-known for delivering an excellent customer experience, but the automaker recently suffered from a data breach that may have exposed some of its customers.