How Apple is Battling Phishing Scams and Protecting Your Personal Data
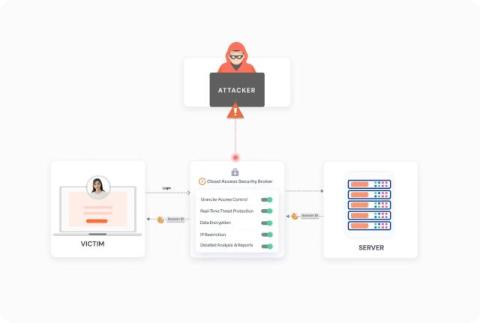
The digital world is now facing a serious challenge of phishing where fraudsters employ fake emails, websites or links to get confidential data which can result into great losses if not well handled. Apple, however, has taken several steps to protect users from these attacks.