Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Devo Multitenancy Provides Fast, Secure, Self-Service Access to Data Across Multiple Tenants
Security teams need the ability to model their complex organizations by splitting data across multiple tenants while maintaining complete visibility throughout the entire infrastructure. At the same time, they must keep data segregated to maintain security and meet data residency and compliance requirements.
Log Management for Shared Responsibility Model Compliance
Russian Cyberwar Attacks Against U.S. Put Added Pressure on SOC Teams
The Russian cyberattacks against the U.S. are ramping up in scope and volume. Last month, a hacking group claimed credit for cyberattacks hitting more than a dozen U.S. airports’ websites, temporarily rendering parts of the sites inaccessible to the public. State-sponsored actives in non-war conditions expend exorbitant efforts to disguise themselves to prevent attribution. They also purposefully limit the scope of their attacks.
Insights from Dolby and AWS CISOs on the challenges and opportunities in orchestrating the defense of modern applications
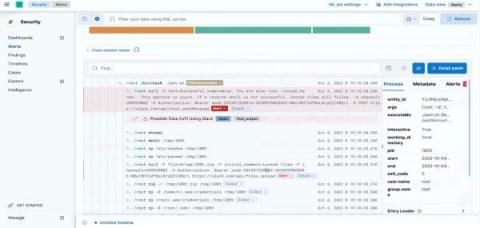
Elastic Security furthers unification of SIEM and on-host protection with XDR, cloud, and endpoint security
Planning Your Log Collection
Centralized Log Management for Incident Response
Leading financial institutions hedge risk by focusing on these 5 critical SIEM requirements
Six SIEM Essentials for Successful SOCs
A few weeks ago, Gartner named Splunk Enterprise Security a Leader in the 2022 Gartner® Magic Quadrant™ for SIEM. This is the ninth consecutive year that Splunk has been placed in the Leader’s quadrant. We’re honored to be recognized and we believe our placement is a testament to our commitment to delivering a data-centric security analytics solution that accelerates threat detection and investigations.