Easily ingest and monitor security logs with Cloud SIEM Content Packs
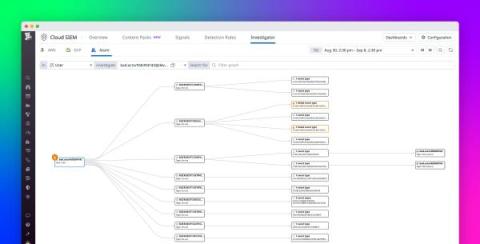
Datadog Cloud SIEM helps customers protect their cloud environment and SaaS applications against threats with built-in threat detection rules, interactive dashboards, workflow blueprints, and in-depth support resources. These capabilities provide valuable insights into your security posture, so you can respond promptly to emerging threats. In order to generate these insights, Cloud SIEM analyzes log data, which users can start sending to Datadog by enabling one of our out-of-the-box integrations.